Executive Summary
Agent pipelines show up when the single-agent demo starts colliding with multi-step, multi-system reality. The gap isn’t theoretical; it’s the space between a model that can summarize emails and a business process that needs retrieval, routing, action, and audit with acceptable latency and cost.
Once a workflow touches customer data, money movement, or compliance logging, orchestration becomes non-optional. Pipelines provide the structure to enforce handoffs, isolate failures, and meter tokens and time. They also introduce new points of friction: state management, dependency control, and evaluation in context rather than per-step.
Most teams find the hard part isn’t the model but the glue. The pressure is to make AI automation use cases resilient without neutering their usefulness. That means leaning into contracts, queues, and gates, and accepting that some autonomy needs a leash.
Expect iterative refactors. You’ll ship a thin pipeline, watch it buckle under variance, then add boundaries and metrics until it stops waking people up at 2 a.m. The cost of getting this wrong is operational, not academic.
Introduction
A support workflow started dropping escalations on Fridays. Nothing obvious broke—no alarms, no CPU spikes—but customers waited hours. Digging in, we found an LLM-driven classifier stuck behind a retriever that intermittently timed out when a cache warmed slowly. The fallback kicked in, but downstream scripts didn’t respect the degraded mode and queued work as if nothing changed.
That’s how Engineering Agent Pipelines for AI Automation Use Cases became a requirement. A handful of loosely-coupled agents had silently turned into a production system without pipeline discipline. Latency stacks, token budgets, third-party limits, and soft failures added up. AI automation use cases are sensitive to this because the variability inside models magnifies any orchestration wobble.
Operational pressure forces boundaries around agent behavior
In production, agent pipelines look less like clever chatbots and more like disciplined assembly lines. Each step has a contract: expected inputs, allowed side effects, time limits, and what happens when things go sideways. The pipeline exists to keep decisions local, isolate failure domains, and maintain an audit trail when judgment calls are handed to models.
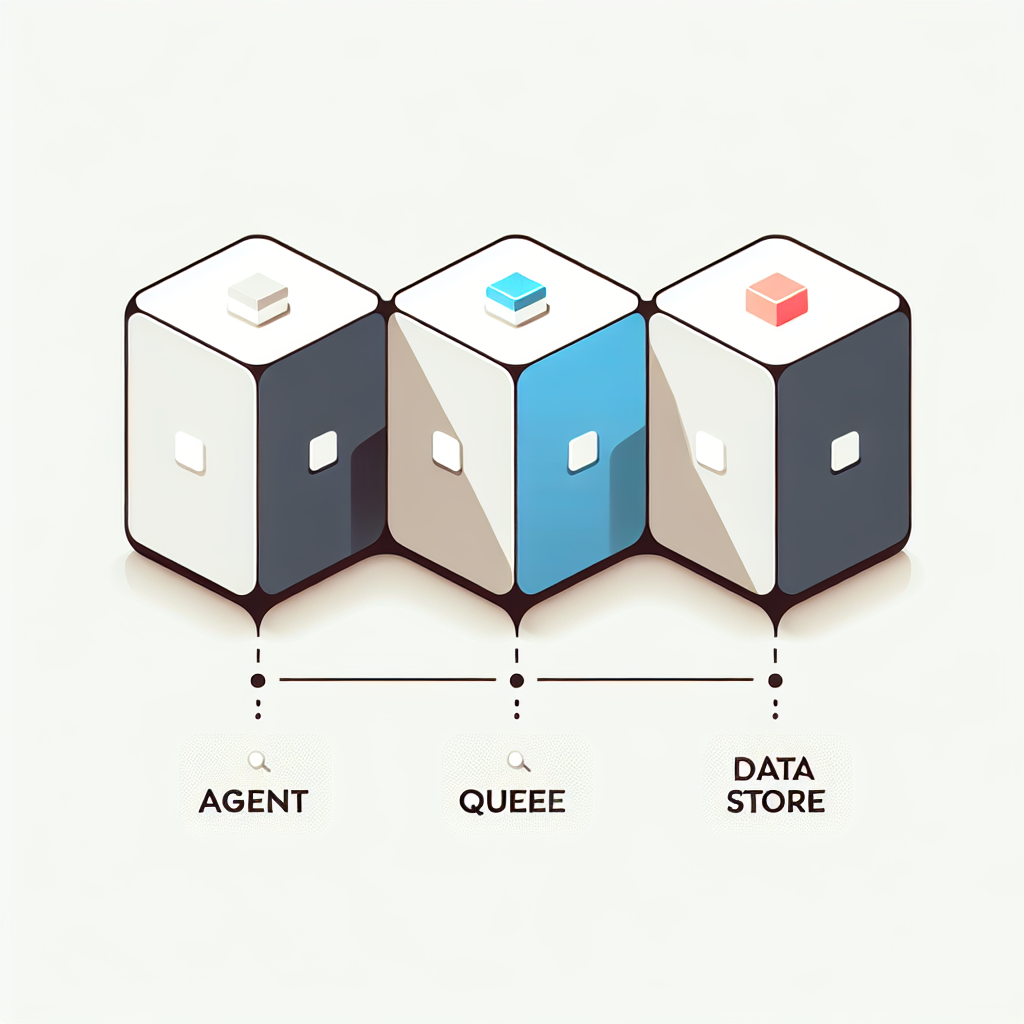
The core boundary is state. Agents are happy to improvise; systems aren’t. You’ll need a minimal state store that tracks job intent, intermediate artifacts, and outcome verdicts. Without it, retries become replayed hallucinations, and you can’t explain why a customer got the result they did.
Second boundary: resource policing. Tokens, latency, and external API quotas must be budgeted per stage. If you don’t meter, one noisy data source or a drifted prompt blows up cost and puts a natural language model in charge of throughput. A lightweight budget gate per stage prevents cross-contamination of pain.
Third boundary: side-effect control. Anything that writes—emails, tickets, transactions—should be separated from anything that reasons. Reasoning agents propose; effectors act with constraints. This split is tedious but necessary. When a model gets chatty at 5 p.m., the worst case becomes extra proposals, not exploding external systems.
Failure modes are boring and frequent: missing schemas in retrieved context; stale tools; drifting prompts; nondeterministic dependencies; partial writes with successful upstream steps. You will see two kinds of breakage: predictable overload and rare edge cases that only appear in production data. The pipeline’s job is to turn both into contained incidents with clear blast radius.
Contracts at each hop reduce downstream guesswork
Define payload shapes, confidence thresholds, and allowed fallbacks. Avoid implicit behavior wired into prompts. If an agent’s contract says “return a structured proposal and a confidence score,” downstream logic can decide whether to proceed or escalate without parsing prose for intent.
Cost and latency gates shape topology
Set ceilings for each stage and make them visible. Gates drive design choices: you might move an expensive reasoning step behind a cheap filter, or batch context retrieval. Topology follows the money and the minutes more than it follows elegance.
Guardrails versus adaptability: picking the leak path
Too much guardrail turns agents into brittle scripts; too little creates unpredictable side effects. Decide where you permit variance: often on proposals, never on final writes. Allow agents to explore, but make the last mile deterministic.
Sequencing work across environments without losing control
Pipelines unfold across dev, staging, and production with different data realities. Sequencing, handoffs, and dependencies matter more than model choice. The work starts with intake normalization, then context retrieval, then reasoning, then effectors, then feedback and metrics routing back into evaluation.
Intake normalization is where many teams slow down. Real inputs are messy: partial data, varied formats, and downstream assumptions that crept into prompts. A normalization pre-stage hardens inputs and removes trivial errors so the expensive steps aren’t cleaning up basic issues.
Context retrieval gets political. Data owners want control, but your agents need relevant facts fast. You’ll debate whether to centralize features or let agents pull what they need. Dependencies here are subtle: schema versioning, caching policy, and the security model on data pulls. Revisions often happen after a small outage reveals you’ve granted too many read paths.
Reasoning is where teams revisit decisions about prompts, tools, and temperature under load. If you deploy a new prompt variant, your latency and cost graphs will tell you whether you guessed correctly. Dependencies include tool availability, updated function signatures, and external rate limits. The friction becomes negotiating safety thresholds with product when the agent gets smarter but slower.
Effectors decide what can be batched, what demands synchronous confirmation, and what must be queued for a human gate. Handoffs fail when an effector assumes the proposal is already validated; they succeed when an explicit validator enforces policy and blocks bad writes.
Finally, feedback. A pipeline that doesn’t feed outcomes back into evaluation is a black box. Metrics should connect to decisions: how many proposals were rejected, which context sources correlate with high-confidence outputs, where cost spiked. Teams slow down here if they treat evaluation as a weekly report instead of a live circuit breaker.
Choosing infrastructure that won’t collapse under variant workloads
Tool choices are constrained by the kind of risk you can tolerate. If your workload has bursty traffic, you’ll prefer a queue that can buffer spikes and a scheduler that supports backpressure, not just retries. If latency drives revenue, you’ll bias toward in-memory state for fast reads and write-ahead logs for safe restarts.
For agent coordination, use an orchestrator that treats each stage as a unit with a transaction boundary. You need explicit timeouts, compensations, and visibility into running jobs. The simpler the execution model, the easier it is to reason about failures.
Context storage becomes a trade-off between freshness and retrieval cost. A hybrid approach—short-lived caches for hot data, durable stores for canonical records—keeps reasoning steps fed without hammering primary systems. Vector search helps with recall but introduces versioning and drift concerns; treat it like a derived index with regular rebuilds.
Secrets and policy enforcement sit under everything. If agents call external services, rotate credentials and restrict scopes. When you wire tools into reasoning, ensure function signatures include explicit constraints. It’s not glamorous, but it’s the difference between a controlled failure and a public incident.
Concrete AI automation use cases that strain naive designs
Invoice reconciliation looks simple until exception handling dominates. A basic agent can match line items and flag mismatches. In reality, vendor formats drift, tax rules change, and partial data arrives late. The pipeline needs a guard stage to detect when context is insufficient and route to a human queue. Trade-off: stricter gating reduces bad payouts but increases manual workload during quarter-end spikes.
Outbound prospecting feels like a throughput game until reputation gets involved. A reasoning agent crafts messages; an effector sends them. If deliverability drops, the pipeline must throttle based on feedback signals and switch templates. Unintended consequence: agents that optimize for short-term responses will degrade long-term domain health unless the pipeline enforces pacing and content diversity.
Tier-1 support deflection is seductive until the first compliance incident. A classifier and responder can resolve common tickets, but if the pipeline doesn’t enforce sensitive data handling, agents will echo prohibited information. The trade-off sits between accuracy and policy: you’ll accept more handoffs to humans in exchange for a predictable compliance posture.
Operational monitoring is itself an AI automation use case. Agents analyze logs and alerts, propose remediations, and sometimes act. The pipeline has to sandbox actions, record proposals, and require confirmations for anything beyond safe operations. Side effect: when incidents escalate, human responders expect clear narratives; agent pipelines that skip proposal logging turn into forensics nightmares.
Where newcomers stumble and where veterans still slow down
This table isn’t a summary; it’s a set of decision points that change how your pipeline behaves when reality hits.
Decision area Newcomer impact Experienced impact State management Implicit state leads to unreproducible errors and messy retries Explicit job state enables targeted rollbacks and audit trails Budget gating Unbounded tokens/latency cause cost spikes and SLA misses Per-stage ceilings drive topology and keep throughput stable Effectors vs reasoning Combined steps create silent side effects and hard-to-debug writes Separated roles limit blast radius and simplify incident response Context retrieval Direct reads from source systems stall under load Derived indexes and caches protect primaries and control drift Evaluation Offline reports fail to catch live regressions Inline metrics trigger safe fallbacks before customers notice
Questions that surface once pilots touch production
How do we prevent expensive steps from dominating cost? Put a cheap gate in front of expensive reasoning. Filter obvious negatives, batch where possible, and enforce per-stage budgets. Treat spikes as signals to re-sequence, not just to optimize prompts.
What’s the minimal audit trail that keeps us safe? Record inputs, proposals, decisions, and side effects per job. You don’t need a full transcript, but you do need enough to reconstruct why an action happened and who approved it—human or policy.
How do we handle variability without constant prompt surgery? Stabilize inputs and tools first. If prompts are doing cleaning and policy enforcement, move that work into pre-stages and validators. Then adjust prompts for clarity, not for operational control.
When do we allow agents to act autonomously? Only in domains where the cost of a wrong action is tolerable and reversible. Autonomy belongs in proposals and low-risk effectors; the pipeline should require confirmation for anything with lasting impact.
What breaks during scale-out? Cache invalidation, schema drift, and overlooked quotas. Build for graceful degradation: partial context, bounded retries, and a clear fallback mode that downstream stages respect.
Accountability shifts from individual models to the pipeline edges
Given how things behave today, the next quiet change is treating pipelines as the product. Models become interchangeable components; contracts, gates, and effectors carry the responsibility. Incidents will be framed as pipeline failures, not model errors.
Scripts -> Ad-hoc Agents -> Coordinated Pipelines -> Governed Automation